Don’t Get Scammed / Phished by Look-Alike Emails (PayPal Example)
See Apple Mail Security: Viewing Mail Headers for how to configure Apple Mail to make most phishing emails obvious as well as the UPS example.
...
Phishing is the attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money), often for malicious reasons, by masquerading as a trustworthy entity in an electronic communication.
Clicking on email links or attached files is risky: merely clicking on a link to go to the claimed site can result in compromising the computer for some users. While Mac users are generally better off, a Mac is no guarantee of safety, and all sorts of nasty tricks can be played on the desgination sites.
Phishing relies on “social engineering”, particularly an emotional reasponse (greed, fear, loyalty, irritation, friendship, authority, desire for help, etc). Often the phishing emails are difficult to distinguish from a legitmate email from the company being imitated and frequently even use the company’s own images from a legitimate server. If a link is clicked on, the destination web site may be a clone of the real one, which makes it even more “real” for the victim.
What you may lose: username and password, security codes, credit card numbers—anything you can be tricked into entering on a phishing site. Or you may have your computer encrypted and subjected to ransom-ware. No fun at all.
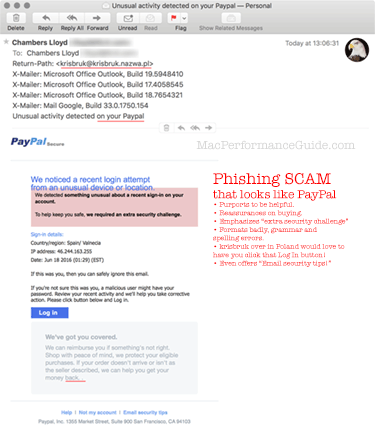
Example — phishing for PayPal information
See also the Amazon phishing example and the security topics page.
This is a good way to lose your money, particularly if linked to your bank account.
- NEVER click on links in emails that you are not 100% certain of from a trusted party beforehand. Particularly on a Windows PC, though Mac users are at risk too.
- Did I mention NEVER CLICK ON LINKS in EMAILS, NO MATTER WHAT? It’s just not worth it.
- Configure your email program so that images do not automatically load in your mail program. If Mail loads images automatically, you’re essentially telling the sender (the criminal sending the email) that s/he’s got a “live one”: you. Ditto for mail on the iPhone or iPad.
- Pay attention to spelling and grammar errors. This example below is unusually good; it has only two obvioius errors in grammar/spelling (but “Valnecia” is another).
- Configure the mail program to show Return-Path and X-Mailer message headers; these sometimes show obvious scammer information.
- Check the "To" address. In this case, the "To" is not an email I use for PayPal—a very common red flag.
The source code to this email tries to disguise itself a bit; it uses https://bit.ly links to hide the true destination of anything clicked upon. This helps it evade some blacklist filters.

 diglloydTools™
diglloydTools™