Risky “Zero Day” Exploit Bugs Fixed in iOS 9.3.5 for iPhone, also in OS X
See also Apple Mail Security: Viewing Mail Headers in the Setting Up Your Mac For Better Security section as well as all security topics.
See my post two days ago on the frustrating experience of trying to update iOS—shame on Apple for making it so hard to install a critical security fix—there are simple ways to fix the software to not stand in the way of updating iOS, if only Apple would do it (e.g., just allow a backup to some other drive).
…
A “zero day” exploit is a security bug that remains unknown to the world at large, including the manufacturer of the device. When a zero day exploit can compromise a system, it can sometimes sell for big money—typically to spy agencies (including our own morally-impaired agencies here in the USA*). Thus some zero-day exploits can be extremely valuable. And potentially fatal, such as to activists whose phone and/or computers are compromised.
ComputerWorld reports in Apple patches iOS security flaws found in spyware targeting activist:
To spy on a human rights activist, hackers allegedly connected to a Middle Eastern government used three previously unknown vulnerabilities in Apple’s iOS.
The claims -- from research at Toronto-based Citizen Lab and mobile security firm Lookout -- focus on spyware that targeted Ahmed Mansoor, an activist in the United Arab Emirates.
Earlier this month, Mansoor received an SMS text message on his iPhone claiming to offer “new secrets” about tortured detainees in his country. However, inside the message was a link that, once clicked, can infect an iPhone with spyware, using three zero-day exploits of iOS, the research found.
The exploits work by remotely jailbreaking the device to secretly download the spyware – which can then access the iPhone’s camera, microphone, and messages.
Lookout called the attack the most sophisticated it’s ever seen on a device. The researchers have already informed Apple about the exploits, and iOS version 9.3.5 -- which was released on Thursday -- fixes the issues. The attack is rare because it used three previously unknown vulnerabilities, suggesting the hackers were well-funded. Just one of these exploits can be worth $1 million.
...
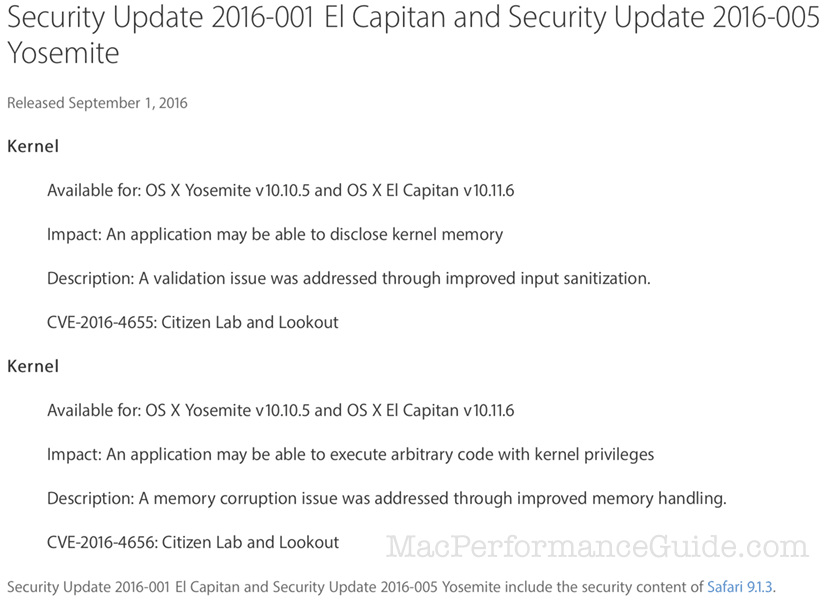
Apple apparently felt strongly enough about the bug to issue an emergency iOS and macOS update—kudos to Apple. Details on the Sept 1 security update page. Be sure to update macOS on your computer, and iOS on your iPhone or iPad.
MPG has long advised not clicking on links in emails or any similar behavior (OTOH, any at-risk activist willing to click on a hyperlink in an email is a sort of Darwinian fool).
This case makes a strong argument for Apple (and other companies) to offer an option so that hyperlinks are disabled in mail messages—why has Apple not done this yet? Such an option could allow a bypass of some kind, such as control-click. It would surely prevent 99.99% of casual users from opening hyperlinks by accident or cluelessness; most users simply cannot be trained to be smart about how to assess the risk. It ought to be standard fare for corporate and government email at the least.
* While tens or hundreds of millions of users may be at risk from a zero-day exploit, this country as yet does not have a policy of protecting people by getting zero day exploits fixed. Rather the NSA and CIA and FBI policies seems to be to exploit the bugs as long as feasible. This is a political and moral question which has arguments on both sides but since foreign governments also adore zero-day exploits, the obligation of our government to protect its own citizens seems to rise to the fore as something worthy of public debate (in Congress).

 diglloydTools™
diglloydTools™