Don’t Assume that a Password Manager is Safe, Auto-Fill for Password a Bad Idea
Security expert Bruce Schneier posted some good info on password managers.
Security is often a trade-off with convenience, and most password managers automatically fill in passwords on browser pages. This turns out to be a difficult thing to do securely, and opens up password managers to attack.
My own password manager, Password Safe, wasn't mentioned in either of these papers. I specifically designed it not to automatically fill. I specifically designed it to be a standalone application. The fast way to transfer a password from Password Safe to a browser page is by using the operating system's cut and paste commands. I still recommend using a password manager, simply because it allows you to choose longer and stronger passwords.
MPG agrees completely that use of a password manager is a big step up in security for most users, because password quality goes way up—relieving the user of the need to think up new and relatively weak passwords and/or struggle with strong but difficult and hard to remember passwords.
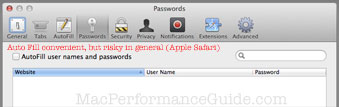
I don’t know if Apple Safari Auto Fill is secure or not. Or if secure, whether if it will stay secure. But this is how I configure Safari.
Is it safe? You never know, and so it is never a good idea.
Auto fill for passwords = risky in general
Free WiFi might be far more costly than you think.
From Password Managers: Attacks and Defenses. Emphasis added. Lots more critical details, but the main thing is that autofill is a dubious idea subject to many risks, and varies by browers and password manager as to the extent of those risks.
As a warm-up we present one example here. Consider web sites that serve a login page over HTTP, but submit the user’s password over HTTPS (a setup intended to prevent an eavesdropper from reading the password but actually leaves the site vulnerable).
Suppose a user, Alice, uses a password manager to save her passwords for these sites At some point later, Alice connects to a rogue WiFi router at a coffee shop. Her browser is directed to a landing page that asks her to agree to the terms of service, as is common in free WiFi hotspots. Unbeknownst to Alice, the landing page contains multiple invisible iFrames pointing to the login pages of the websites for which Alice has saved passwords. When the browser loads these iFrames, the rogue router injects JavaScript into each page and extracts the passwords auto-filled by the password manager.
This simple attack, without any interaction with the user, can automatically extract passwords from the password manager at a rate of about ten passwords per second. Six of the ten password managers we examined were vulnerable to this attack.
From the user’s point of view, she simply visited the landing page of a free WiFi hotspot. There is no visual indication that password extraction is taking place.
...
Chrome (all platforms) is the only automatic autofill password manager that is not vulnerable to the iFrame-based attack, because they never automatically autofill passwords in iFrames. All the other automatic autofill password managers are vulnerable to this attack. Even though the autofill policies of Norton IdentitySafe, Safari, Mobile Safari, and LastPass Tab described in Sec- tion 2.2 restrict the number of passwords that can be stolen in a single sweep to 1, they remain vulnerable.
Password sync across devices (e.g. desktop computer and iPad/iPhone) is a risky thing too, for reasons the paper discusses.
We disclosed our results to the password manager vendors, prompting several changes to autofill policies. Due to our findings, LastPass will no longer automatically autofill password fields in iFrames, and 1Password will no longer offer to fill passwords from HTTPS pages on HTTP pages.
Emperor’s new Password manager
A video explaining some vulnerabilities. Again, auto-fill is a bad idea, but there is more than that.

 diglloydTools™
diglloydTools™











